Recently, we have received an increasing number of inquiries regarding an adjustment in TLS certificate validation—particularly in connection with a notification that appears after updating to newer anynode versions.
Since version 4.12.27 (available since September 2025), the following applies:
anynode no longer evaluates the Extended Key Usage (EKU) by default
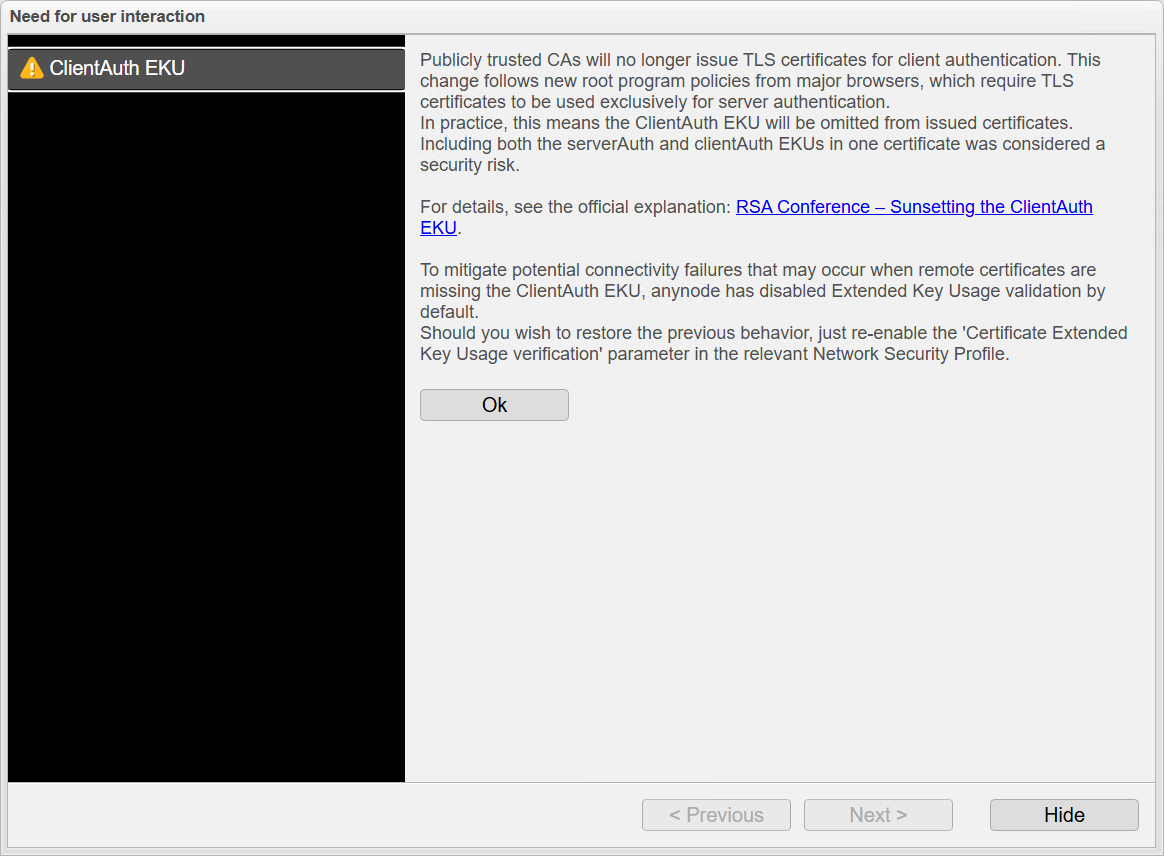
Users performing an anynode update are informed by the following message:
What is the reason behind this?
This change is driven by new root program policies introduced by major browser vendors. As a result, publicly trusted certificate authorities (CAs) no longer issue TLS certificates for client authentication, or the EKU field “clientAuthentication” is increasingly being omitted.
Additionally, combining serverAuth and clientAuth within a single certificate has been classified as a security risk.
Why was the validation adjusted?
A strict EKU check would nowadays, in many cases, result in valid and modern certificates being rejected—especially when the “clientAuthentication” EKU is missing.
To avoid connection issues, EKU validation has therefore been disabled by default in anynode.
What does this mean in practice?
- Certificates without the “clientAuthentication” EKU are still accepted
- Compatibility with current PKI standards is ensured
- Security continues to rely on the trust chain and certificate validity
What actions are required by the user?
The informational message shown during login in the anynode frontend only needs to be acknowledged once.
Optional: Restore previous behavior
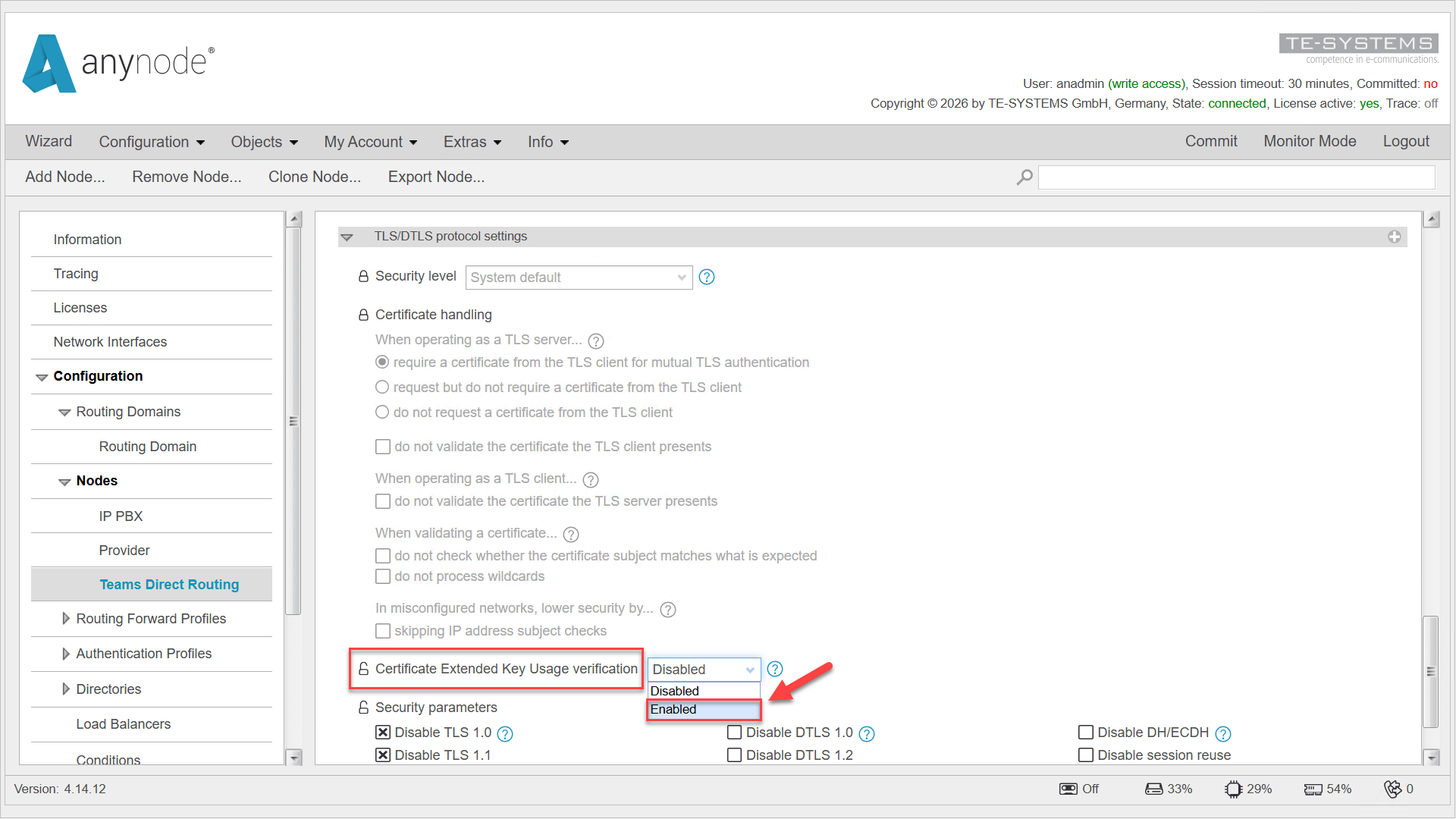
If required, EKU validation can still be enabled:
Parameter “Certificate Extended Key Usage verification” in the respective network security profile is set to enabled.
Get more official details here: